Introduction to Nmap ARP scan
ARP (Address Resolution Protocol) is a low level protocol working at Link layer level of the Internet Model or Internet protocol suite which was explained at the Nmap Basics introduction. There are other 3 upper layers: the Internet layer, the Transport layer and the Application layer.
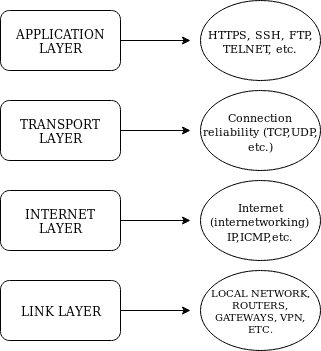
Image source: https://linuxhint.com/nmap_basics_tutorial
Note: some experts describe the Internet Model with 5 layers including the physical layer while other experts claim the Physical Layer doesn’t belong to the Internet Model, this Physical Layer is irrelevant to us for Nmap.
The Link Layer is a protocol used in IPv4 local networks to discover online hosts, it can’t isn’t used on the internet and is limited to local devices, it is either used in IPv6 networks in which the NDP (Neighbor Discovery) protocol replaces the ARP Protocol.
When using Nmap on a local network ARP protocol is applied by default for being faster and more reliable according to the official data , you can use the flag –send-ip to force Nmap to use the Internet Protocol within a local network, you can prevent Nmap from sending ARP ping by using the option –disable-arp-ping too.
Nping ARP scan types
Former Nmap versions came with a variety of options to carry out ARP scans, currently Nmap doesn’t support these flags which are now usable through the tool Nping included in Nmap, if you have Nmap installed you already have this tool.
Nping allows to generate packet under many protocols, as it official website describes it can also be used for ARP poisoning, Denial of Service and more. Its website lists the following features:
- Custom TCP, UDP, ICMP and ARP packet generation.
- Support for multiple target host specification.
- Support for multiple target port specification.
- Unprivileged modes for non-root users.
- Echo mode for advanced troubleshooting and discovery.
- Support for Ethernet frame generation.
- Support for IPv6 (currently experimental).
- Runs on Linux, Mac OS and MS Windows.
- Route tracing capabilities.
- Highly customizable.
- Free and open-source.
(Source https://nmap.org/nping/)
Relevant protocols for this tutorial:
ARP: a regular ARP packet request looks for the MAC address using the device’s IP address. (https://tools.ietf.org/html/rfc6747)
RARP: a RARP (Reverse ARP) request resolves the IP address by using the MAC address, this protocol is obsolete. (https://tools.ietf.org/html/rfc1931)
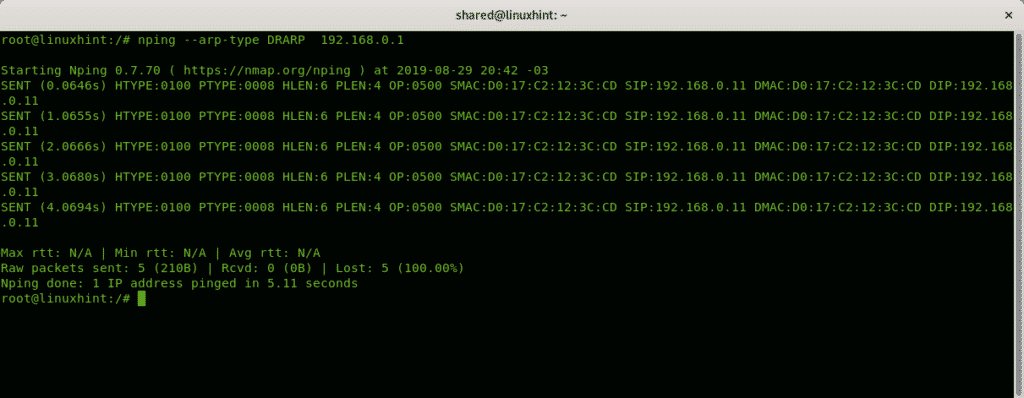
DRARP: a DRARP (Dynamic RARP) protocol, or protocol extension developed to assign dynamic IP address based on the physical address of a device, it can be used to obtain the IP address too. (https://tools.ietf.org/html/rfc1931)
InARP: an InARP (Inverse ARP) request resolves the DLCI (Data Link Connection Identifier) address which is similar to a MAC address. (https://tools.ietf.org/html/rfc2390)
Basic examples of ARP, DRARP and InARP packets:
The following example sends an ARP request to learn the router MAC address:
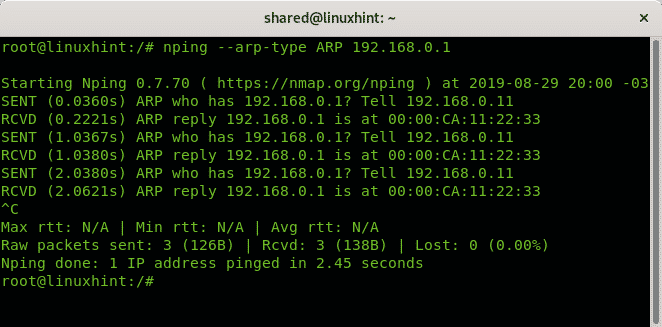
As you can see the –arp-type ARP flag returned the target’s MAC address 00:00:CA:11:22:33
The following example will print information on the protocol, physical and IP addresses of interacting devices:
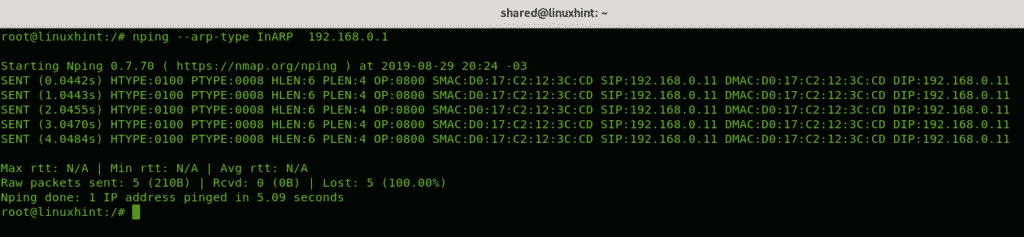
Where:
HTYPE: Hardware Type.
PTYPE: Protocol Type.
HLEN: Hardware Address Length. (6 bits for MAC address)
PLEN: Protocol Address Length. (4 bits for IPv4)
SIP: Source IP Address.
SMAC: Source Mac Address.
DMAC: Destination Mac Address.
DIP: Destination IP Address.
The following example returns the same output:
Nmap ARP discovery
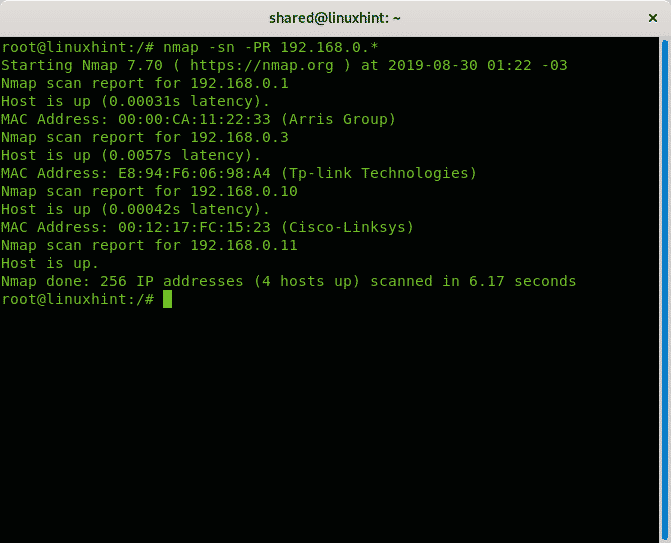
The following example using nmap is an ARP ping scan omitting against all possibilities of the last octet, by using the wildcard (*), you can also set ranges separated by hyphens.
Where:
-sP: Ping scans the network, listing machines that respond to ping.
-PR: ARP discovery
The following example is an ARP scan against all possibilities of the last octet including port scan.
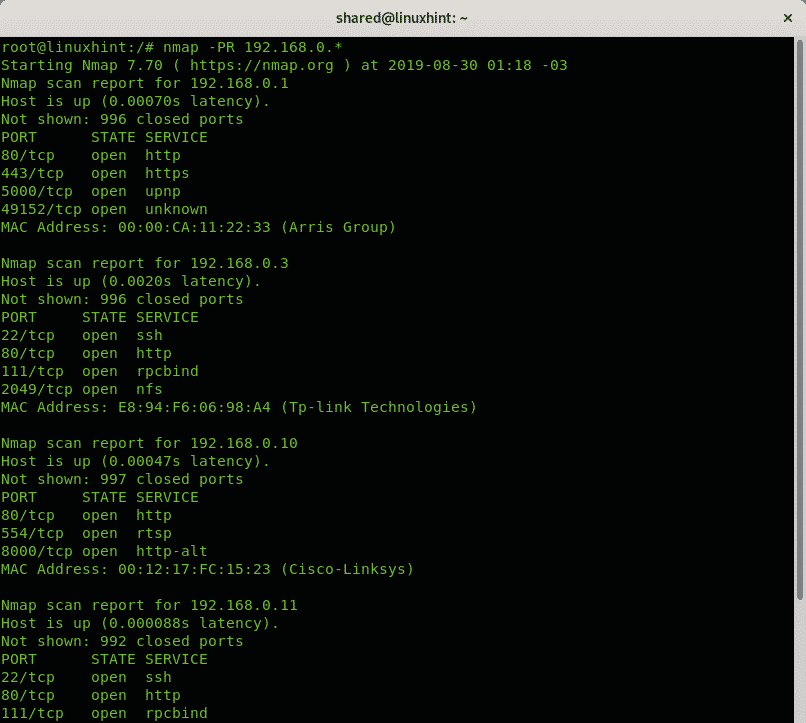
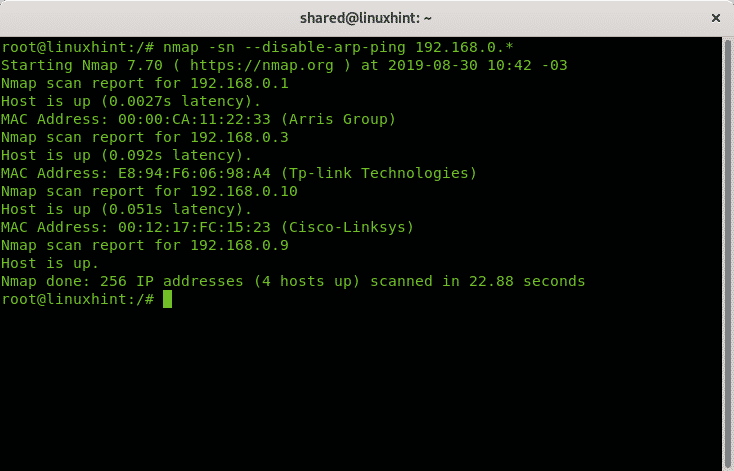
The following example shows an ARP scan against all possibilities of the last octet
The following scan forces and ip scan over an arp scan, again the last octet using the wildcard.
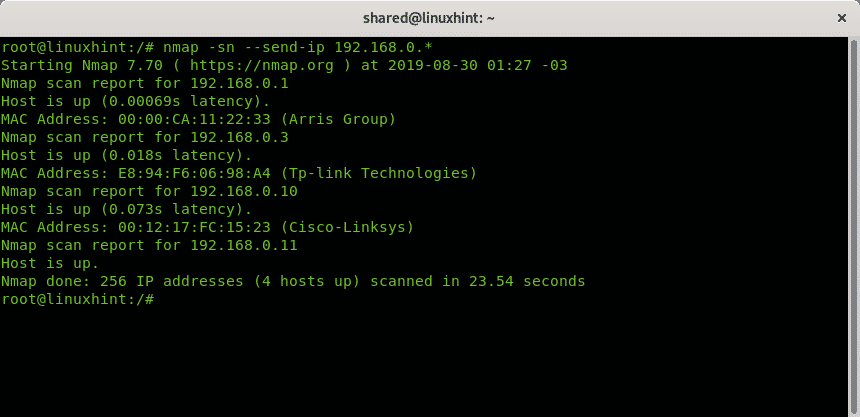
As you can see while the scan made before took 6 seconds it took 23.
A similar output and timing happen if you disable the ARP protocol by adding the –disable-arp-ping flag:
Conclusion
Nmap and Nping ARP scans are ok to discover hosts, while according to the official documentation the programs may be useful for DoS, ARP Poisoning and other attack techniques my tests didn’t work, there are better tools focused on the ARP protocol like ARP spoofing, Ettercap,or arp-scan which deserve more attention regarding this aspect. Yet when using Nmap or Nping, the ARP protocol adds the scan process the trustability of tagging packets as local network traffic for which routers or firewalls show more patience than for external traffic, of course this won’t help if you flood the network with packets. ARP modes and types are not longer useful under Nmap but all documentation is still useful if applied to Nping.
I hope you found this introduction to Nmap and Nping ARP scan useful. Keep following LinuxHint for more tips and updates on Linux and networking.