While the protocol AH is an authentication protocol, the ESP protocol provides authentication and encryption too.
Security Association:
The association consists in the keys administration and establishing a secure connection between the devices, this is the first step in a connection and is carried out by the protocol IKE (Internet Key Exchange).
Authentication:
In this case the authentication does not provide encryption because the information is not ciphered, the function of the AH protocol and it’s authentication is to confirm the delivered packet wasn’t intercepted and modified or “broken” during the transference. The AH protocol helps to verify the transferred data integrity and the implicated IP addresses. Using IPSEC with AH won’t protect our information from a Man In the Middle attack but it will let us know about it by detecting differences between the received IP packet’s header and the original one. To do it the AH protocols identifies packets adding a layer with a sequence of numbers.
AH, Authentication Header as its name specifies also verifies the IP header layer, while the ESP doesn’t include the IP header.
Note: IP Header is an IP’s packet layer containing information on the established connection (or going to get connected), such as the source and destination address among more.
Encryption :
In contrast to the protocol AH which only authenticates the integrity of the packets, senders in IP headers, ESP (Encapsulating Security Payload) packet additionally offers encryption which means if an attacker intercepts the packet he won’t be able to see the content because it is ciphered.
Asymmetric and Symmetric encryptions
IPSEC combines both asymmetric and symmetric encryptions to provide security while keeping speed.
Symmetric encryptions have a single key shared between users, while asymmetric encryption is the one we use when authenticating with public and private keys. The asymmetric encryption is safer because it allows us to share a public key with many users while the security relies on the private key, symmetric encryption is less safe because we are forced to share the only key.
Symmetric encryption advantage is the speed, a permanent interaction between two devices permanently authenticating with asymmetric encryption would be slow. IPSEC integrates both of them, first the asymmetric encryption authenticates and establishes a safe connection between the devices using protocols IKE and AH and then it changes to symmetric encryption to keep the connection speed, the SSL protocol also integrates both asymmetric and symmetric encryptions but SSL or TLS belong to higher layer of the IP protocol, that’s why IPSEC can be used for TCP or UDP (you can also use SSL or TLS but is not the norm).
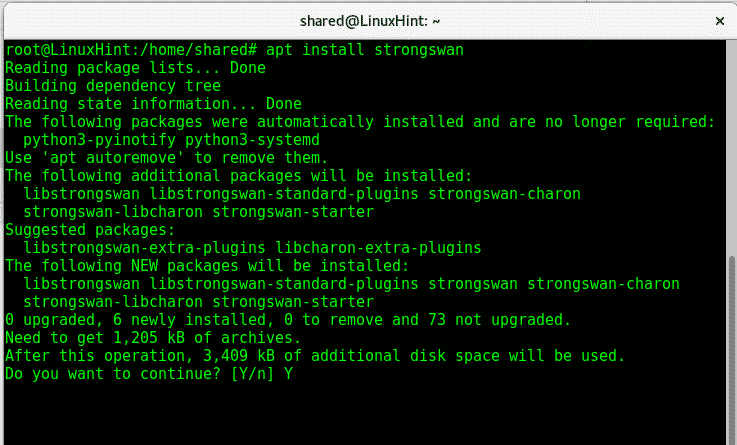
Using IPSEC is an example of the need to add additional support to our kernel to be used as explained in a previous article on the Linux Kernel. You can implement IPSEC on Linux with strongSwan, on Debian and Ubuntu systems you can type:
An article was also published on VPN services including IPSEC easy to setup on Ubuntu.
I hope you found this article useful to understand IPSEC protocols and how they work. Keep following LinuxHint for more tips and updates on Linux.









